Every developer.
Every tool.That's a security failure.
MCPAmbassador is a tool multiplexer. Your developers install one client — their unique key determines which tools appear. Not which MCP servers. Which tools. Pulled selectively from any combination of MCP servers, composed into a single, role-specific toolset, delivered on connection.
A junior dev gets read-only database access, issue tracking, and test runners. A DevOps lead gets deployment pipelines, infrastructure provisioning, and production credentials. Same endpoint. Entirely different tool surfaces.
{ "mcpServers": { "ambassador": { "command": "npx", "args": ["-y", "@mcpambassador/client"], "env": { "MCP_AMBASSADOR_PRESHARED_KEY": "amb_pk_your_key" } } }}The per-user toolset problem — solved
Every developer reaching the same MCP tools is a governance and security failure. Different roles need different tool surfaces.
Without MCPAmbassador
- Every developer installs every MCP on every machine — VS Code, Claude Code, each AI tool separately. Config drift starts on day one.
- Your QA engineer and your infra lead share the same tools. No per-role tool separation exists.
- API keys live in local config files across every machine with no central visibility and no revocation path.
- Onboarding a new developer means hours of MCP setup — and config drift starts immediately.
- No audit trail — no visibility into which tools are called, by whom, or on which device.
With MCPAmbassador
- Install the MCPAmbassador Client once. Each user’s key determines which tools appear — role-specific, from any combination of MCP servers, on every session.
- A QA engineer gets read-only DB access and Playwright. An infra lead gets AWS and firewall controls. Same server, entirely different tool surfaces.
- Credentials stay in an AES-256-GCM encrypted vault. Developers never see raw API keys.
- New developer onboarding in under 5 minutes — install client, authenticate, tools appear. The admin controls what’s included.
- Every tool call logged: who invoked it, from which device, with what arguments, and what was returned. Kill any tool instantly from the admin dashboard.
Your client. Your tools. Zero bleed.
Provision exactly what each role needs — pulled from any MCP, controlled by admins, invisible to everyone else.
Every client, a different surface. One endpoint for all of them.
The features you'd spec if you were building this yourself
MCPAmbassador 0.8.0-beta.2 ships with a complete enterprise feature set. Apache 2.0. Self-hosted. No feature gates.
Tool Multiplexer
MCPAmbassador composes a bespoke, role-specific tool surface from any number of downstream MCP servers and delivers it through a single client connection. Developers connect once — their authorized tools appear. Admins control which specific tools each user or group receives.
Encrypted Credential Vault
Per-user AES-256-GCM encrypted storage with HKDF key derivation. Credentials are decrypted only at spawn time, injected into the MCP process, and zeroed from memory. Developers never see raw API keys.
Groups & RBAC
Group-based access control. Assign users to groups, assign MCPs to groups. Users see only the MCPs their groups authorize. Role inheritance is additive.
MCP Marketplace
Self-service MCP discovery. Users browse, view full tool lists, subscribe, and select exactly which tools to enable — no tickets, no manual admin provisioning.
Multi-Client Support
One user, many devices. Each client (VS Code, Claude Code, CI agent) has independent MCP subscriptions and tool selections. Revoke one without affecting others.
Kill Switches
Instantly disable any MCP server — or any individual tool within an MCP — from the admin dashboard. Effect is immediate on next tool call. No client restart required.
Audit Logs
Every tool invocation logged: who called what, from which device, with what arguments, and what was returned. JSON structured logs, queryable in the admin portal.
Community Registry
38+ pre-configured MCP server definitions. GitHub, PostgreSQL, Slack, Stripe, Grafana, Notion, and dozens more — spawn commands and env var schemas already defined.
React Admin & User SPA
Full React 19 SPA for both admin and user workflows. MCP catalog management, group RBAC, marketplace, client management, and subscriptions. Dark mode, responsive, accessible.
Single Docker Deploy
Everything runs in one Docker container. Auto-generated TLS certs, auto-run migrations, auto-generated credential keys on first boot. One command to a running gateway.
See it in action
A full React admin and user portal — dark mode, responsive, every feature accessible. No CLI required.
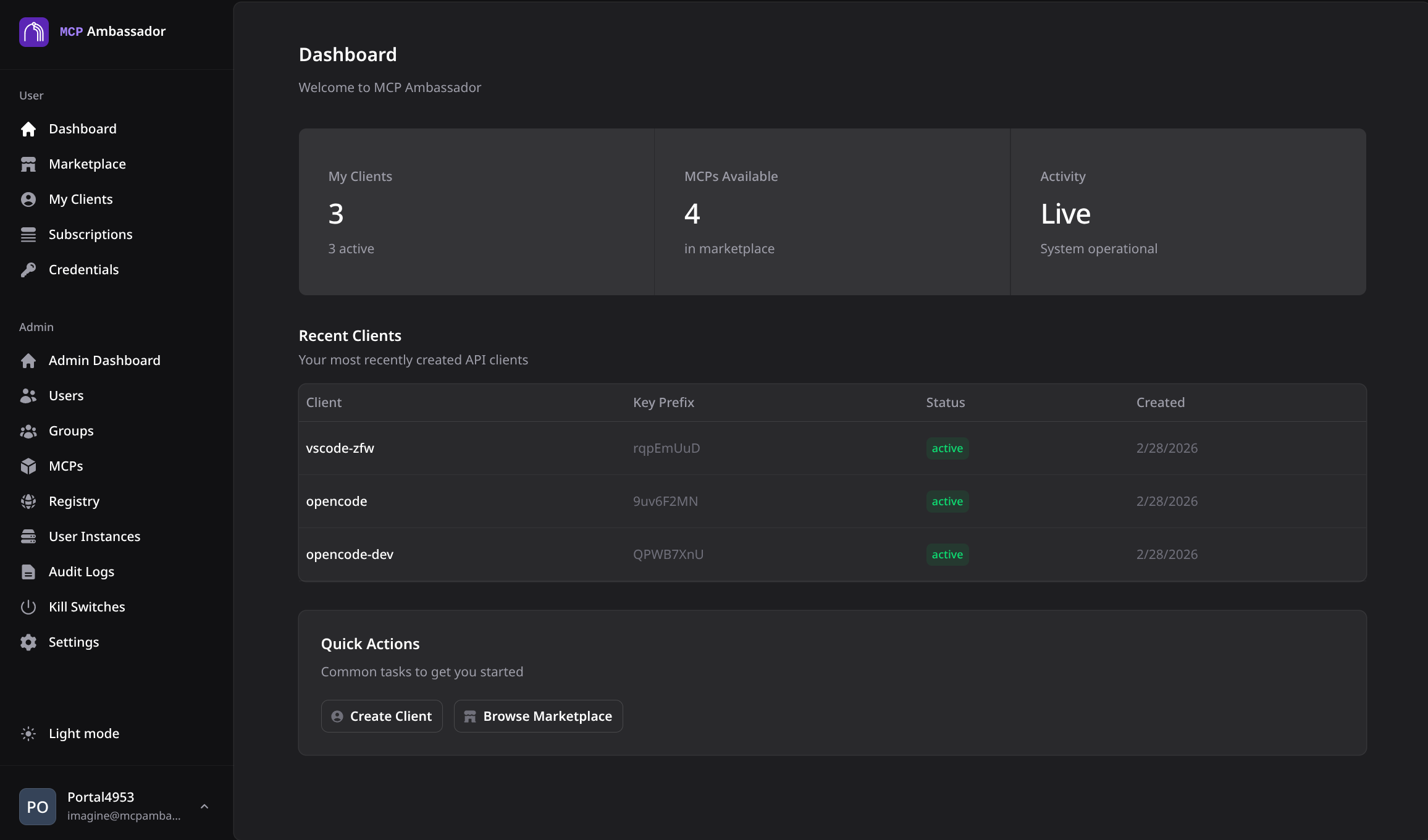
User dashboard with active subscriptions and tool usage overview
38+ MCP servers, pre-configured
The community registry ships spawn commands, environment variable schemas, and tool metadata for every popular MCP server. Admins add them to the catalog in minutes.
AI & Search
Code & Dev Tools
Data & Databases
Documents
Web Automation
Cloud & Infra
Business
Monitoring
Utility
Open source, nothing held back.
Every feature ships free under Apache 2.0. Enterprise capabilities like PostgreSQL, HA, and SSO are on the roadmap — built in partnership with the organizations that need them. Open source, open roadmap.
Open Source
Apache 2.0The full product, self-hosted. No registration required.
- All 0.8.0-beta.2 features included — no gates
- Single Docker container, SQLite backend
- MCP gateway with AAA engine (auth, authz, audit)
- AES-256-GCM encrypted credential vault
- RBAC with group-based access control
- Kill switches — per-MCP and per-tool, effective immediately
- Full audit logs with structured queryable output
- 38+ community registry MCP servers, pre-configured
- React 19 admin and user SPA included
- Unlimited users, clients, and MCP connections
- No registration, no phone-home, no expiry
Enterprise
On the roadmapFor organizations deploying MCP Ambassador under compliance requirements or at a scale that demands PostgreSQL, HA, and SSO. These capabilities are on the roadmap — get in touch to discuss timelines or co-development.
- PostgreSQL backend for production-scale deployments
- High availability with multi-node horizontal scaling
- OIDC / SSO integration (Okta, Entra ID, Auth0, Keycloak)
- SCIM user provisioning
- Federated admin and multi-tenant namespace support
- Advanced compliance audit schemas (SOC 2, ISO 27001, HIPAA)
- Automated credential rotation policies
Ready to give every role its own toolset?
One Docker command. Five minutes to your first curated toolset.
Apache 2.0 · v0.8.0-beta.2 · 327 tests passing · Zero telemetry · Self-hosted
Support the projectBTC: 3QH4WQoQqnhU3LhbZQU8ttXaNco5Ge3xVp·ETH: 0xa5462444c5AEf0B2e32822D9a9B7f91aC794FfF0·GitHub Sponsors